Application security groups
Application security groups enable you to configure network security as a natural extension of an application's structure, allowing you to group virtual machines and define network security policies based on those groups. You can reuse your security policy at scale without manual maintenance of explicit IP addresses. The platform handles the complexity of explicit IP addresses and multiple rule sets, allowing you to focus on your business logic. To better understand application security groups, consider the following example:
In the previous picture, NIC1 and NIC2 are members of the AsgWeb application security group. NIC3 is a member of the AsgLogic application security group. NIC4 is a member of the AsgDb application security group. Though each network interface in this example is a member of only one network security group, a network interface can be a member of multiple application security groups, up to the Azure limits. None of the network interfaces have an associated network security group. NSG1 is associated to both subnets and contains the following rulesDEMO
We will create a Vnet with 3 subnets and host 3 VM's in each subnet. Then we host a default site on VM1 and access it using its private IP inside VM2 and VM3. We then create an ASG and attach it to VM3. Then we configure VM1 to allow traffic only from networks that are associated with the ASG(VM3 in our case)
STEP 1: Create a VNET and 3 Subnets
The total address space is 256(/24 CIDR). Create 3 subnets in the address space
Step 2
RDP into the VM1 and create a default html page. Enable IIS using server manager.
Save it as "index.html" to the path shown below. This path will be only available only after we enable IIS inside the VM.Step 4: Create an ASG and associate it with VM3
Step 5: Create a network rule in VM1 to disallow http traffic from all subnets
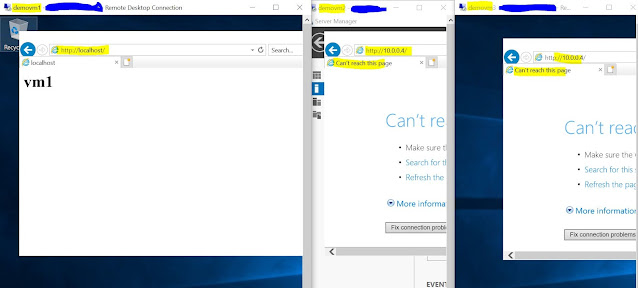
Now we can see that we are unable to access the webpage inside both the VM's.Step 6:
- There are limits to the number of application security groups you can have in a subscription, as well as other limits related to application security groups. For details, see Azure limits.
- In the Azure portal, you can specify only one application security group as the source and destination in a security rule. In the REST API (including PowerShell/Azure CLI), you can specify multiple application security groups in the source or destination.
- All network interfaces assigned to an application security group have to exist in the same virtual network that the first network interface assigned to the application security group is in. For example, if the first network interface assigned to an application security group named AsgWeb is in the virtual network named VNet1, then all subsequent network interfaces assigned to ASGWeb must exist in VNet1. You cannot add network interfaces from different virtual networks to the same application security group.
- If you specify an application security group as the source and destination in a security rule, the network interfaces in both application security groups must exist in the same virtual network. For example, if AsgLogic contained network interfaces from VNet1, and AsgDb contained network interfaces from VNet2, you could not assign AsgLogic as the source and AsgDb as the destination in a rule. All network interfaces for both the source and destination application security groups need to exist in the same virtual network.












Comments
Post a Comment