Why should we cache?
1. Because we dont want to hit the database everytime.
2. Caches store data in memory, so its faster to query them.
3. Caches use a key value pair to store data rather than any complex data structure, So the time complexity is less.
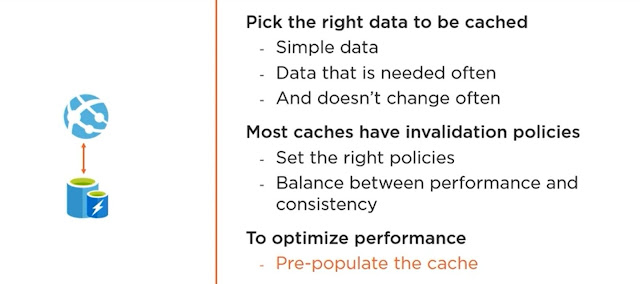
4. Also it improves availability, as if the backend in unavailable we can still get the data from the cache. Not all of it but the most frequently used ones. So its important to make sure that we are caching the right data.
Azure Cache
1. Geo Replication: The main copy remains writable whereas the other copies are maintained as readable. So not only is the data available in a new region but also available in case the primary cache is down. In such a scenario the secondary instance becomes writable.
DATA Types
NUGET
Microsoft.Extensions.Caching.StackExchangeRedis -- allows more data types and operations
services.AddStackExchangeRedisCache(op => {
op.Configuration = "Connection string from azure redis";
});
var data = await distributedCache.GetStringAsync("sales");
if (!string.IsNullOrEmpty(data)) return Ok(JsonConvert.DeserializeObject<IEnumerable<Sales>>(data));
DistributedCacheEntryOptions cacheEntryOptions = new DistributedCacheEntryOptions();
//invalidate or expire the cache after 0 days, 1 minutes and 30 seconds
//absolute expiring will expire the cache after the specified time
cacheEntryOptions.SetAbsoluteExpiration(new System.TimeSpan(0, 1, 30));
//sliding expiration will expire the cache if its not used for the specified time
cacheEntryOptions.SetSlidingExpiration(new System.TimeSpan(0, 20, 0));
var result = SalesdbContext.Sales.Take(20).ToList();
await distributedCache.SetStringAsync("sales", JsonConvert.SerializeObject(result));
return Ok();
While connecting we might get an issue,



Comments
Post a Comment