Create a function App and enable system assigned identity
Create a Keyvault and add a secret (Name in my case)
Configure Access policies for the function app in keyvault
Create an access policy in Key Vault for the application identity you created earlier. Enable the "Get" secret permission on this policy. Do not configure the "authorized application" or applicationId settings, as this is not compatible with a managed identity.
https://docs.microsoft.com/en-us/azure/app-service/app-service-key-vault-references
Key Vault references currently only support system-assigned managed identities. User-assigned identities cannot be used.
We are granting our function app permissions to get and list all the secrets in this keyvault.
Add Key Vault secrets reference in the Function App configuration
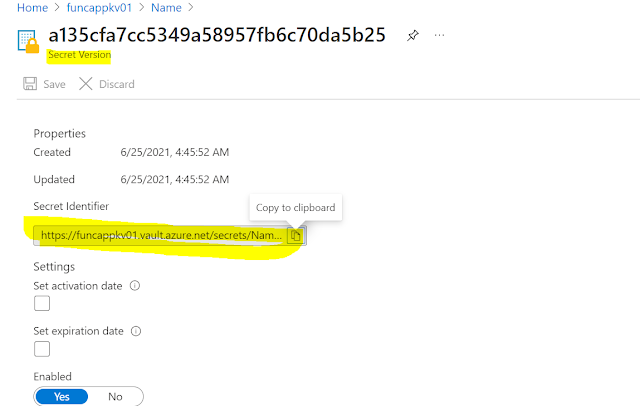
Go to the keyvault and click on the secret we just created.
Copy the secret identifier. We need to add this value to the function app configuration.
Go to the configuration section in the keyvault and add the value.
Now we can directly read the secrets using inside the function app
var password = Environment.GetEnvironmentVariable("mypassword", EnvironmentVariableTarget.Process);






Comments
Post a Comment