Pushing messages to system topics
We do this when the subscribers are azure resources.
Create an azure function that gets triggered when txt files are uploaded to a blob container named container1.
Steps:
1. Create a storage account
2. Create a 2 containers , container1 and container2.
3. Create an azure function
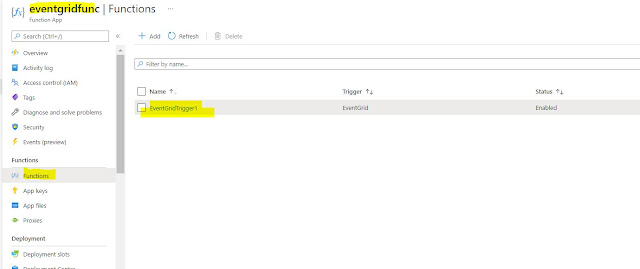
Create a function app and create an event grid triggered function in it.
Create filtering rules in the subscription such that only specific events trigger the azure function. When creating the new subscription we need to create a filter such that only txt files uploaded to container1 trigger the event which in turn would invoke the azure function.
When filtering message based on the container prepend /blobServices/default/containers/{containername}
5. Upload blobs to container1 and 2 of different file formats and notice that only txt file uploaded to container1 trigger the function.
We can do the same thing by going to the portal and creating a event grid system topic and then adding a subscription to it. The easier way is to go to the storage account and add an event subscription under the events menu.
Sending Messages to custom topics
class Program
{
async static Task Main(string[] args)
{
string endpoint = "";
string key = "";
string topicHostName = new Uri(endpoint).Host;
EventGridEvent acct = new EventGridEvent(
id: Guid.NewGuid().ToString(),
subject: "New Account",
data: new {Message = "hi"},
eventType: "NewAccountCreated",
eventTime: DateTime.Now,
dataVersion: "1.0");
TopicCredentials credentials = new TopicCredentials(key);
EventGridClient client = new EventGridClient(credentials);
await client.PublishEventsAsync(topicHostName, new EventGridEvent[] { acct });
}
}
<ItemGroup>
<PackageReference Include="Microsoft.Azure.EventGrid" Version="" />
</ItemGroup>
Receiver
using System;
using System.Collections.Generic;
using System.Linq;
using System.Threading.Tasks;
using System.IO;
using Microsoft.AspNetCore.Mvc;
using Microsoft.Extensions.Logging;
using Microsoft.Azure.EventGrid.Models;
using Newtonsoft.Json;
using Newtonsoft.Json.Linq;
namespace SendNotification.Controllers
{
[ApiController]
[Route("[controller]")]
public class SendNotificationController : ControllerBase
{
// from example at: https://github.com/Azure-Samples/azure-event-grid-viewer/blob/main/viewer/Controllers/UpdatesController.cs
private bool EventTypeSubcriptionValidation
=> HttpContext.Request.Headers["aeg-event-type"].FirstOrDefault() ==
"SubscriptionValidation";
private bool EventTypeNotification
=> HttpContext.Request.Headers["aeg-event-type"].FirstOrDefault() ==
"Notification";
private readonly ILogger<SendNotificationController> _logger;
public SendNotificationController(ILogger<SendNotificationController> logger)
{
_logger = logger;
}
[HttpPost]
public async Task<IActionResult> Post()
{
using (var requestStream = new StreamReader(Request.Body))
{
var bodyJson = await requestStream.ReadToEndAsync();
var events = JsonConvert.DeserializeObject<List<EventGridEvent>>(bodyJson);
if (EventTypeSubcriptionValidation)
{
var subValidationEventData =
((JObject)events.First().Data).ToObject<SubscriptionValidationEventData>();
return new OkObjectResult(
new SubscriptionValidationResponse(subValidationEventData.ValidationCode)
);
}
else if (EventTypeNotification)
{
var notificationEvent = events.First();
_logger.LogInformation(notificationEvent.Subject);
return new OkResult();
}
}
return new BadRequestResult();
}
}
}






Comments
Post a Comment