1. Create a FunctionApp and add a system assigned identity to it. Create on the search bar and select func app. The go to the identity section and turn on the status button. This creates an identity and registers the func app in azure ad. Now we need to grant this identity permissions to read from KV
2. Create a Keyvault and create a secret. I have created 2 (Name = Anish and surname = Aravind)
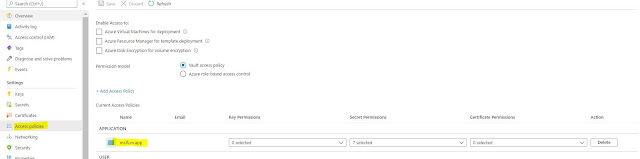
3. Give the function app identity access to read the secrets from Keyvault
4. Select the certificates drop down and select Get and List. Since we need to read the secrets.
5. Save the changes
6. Go to the Configuration section in the function app and add the following values. Cliick on create new application setting. The setting is a key value pair. I have created 2 because I need to read 2 secrets from KV. The application setting key will be the key for the secret in KV.
Name : @Microsoft.KeyVault(SecretUri=secretidentifierfor the secret)
To get the secret identifier for the secret. Go to KV and click on the current version.
This takes you to a new blade. Copy the secret identifier and use it as the value for the application setting that we created.
Key -- name of the secret
Value -- @Microsoft.KeyVault(SecretUri=secretidentifierfor the secret)
Now simply read the values from keyvault as environment variables.
public static class Function1
{
[FunctionName("Function1")]
public static async Task<IActionResult> Run(
[HttpTrigger(AuthorizationLevel.Function, "get", "post", Route = null)] HttpRequest req,
ILogger log)
{
log.LogInformation("C# HTTP trigger function processed a request.");
log.LogInformation("C# HTTP trigger function processed a request.");
{
[FunctionName("Function1")]
public static async Task<IActionResult> Run(
[HttpTrigger(AuthorizationLevel.Function, "get", "post", Route = null)] HttpRequest req,
ILogger log)
{
log.LogInformation("C# HTTP trigger function processed a request.");
log.LogInformation("C# HTTP trigger function processed a request.");
var name = Environment.GetEnvironmentVariable("Name", EnvironmentVariableTarget.Process);
var surname = Environment.GetEnvironmentVariable("surname", EnvironmentVariableTarget.Process);
return new OkObjectResult($"Name {name}, Surname {surname}");
}
}
}
}
Output:








Comments
Post a Comment